Guest blog courtesy of Skyhawk Security.
Skyhawk Security’s Continuous Autonomous Purple Team enables organizations to take a proactive approach to cloud security, preempting threats so security teams can be prepared for what threat actors are going to do. Through AI-based rehearsals, which leverage a Simulation Twin so there is no impact to production, the platform is able to prepare verified automated response and advanced cloud threat detections. These early detections ensure that when certain behaviors or events happen, an alert can be promoted faster, to stop cloud threats from becoming cloud breaches.
What is Autonomous Adversarial Emulation?
Autonomous Adversarial Emulation (AAE) is an emerging security technology that combines predictive machine learning models with historical and simulated threat actor behavior to perform real-time emulation and simulation of cyberattacks. These solutions employ generative models and may utilize autonomous AI agents that are context aware and carry out specific tasks and objectives.
According to Gartner®, “With the increasing use of generative AI by threat actors, hyperautomated cyber-attack prevention solutions are vital for neutralizing threats before they cause harm. Product leaders must integrate preemptive cybersecurity technologies into their offerings now to maintain a competitive edge.”
Continuous Autonomous Purple Team delivers a proactive approach to cloud security
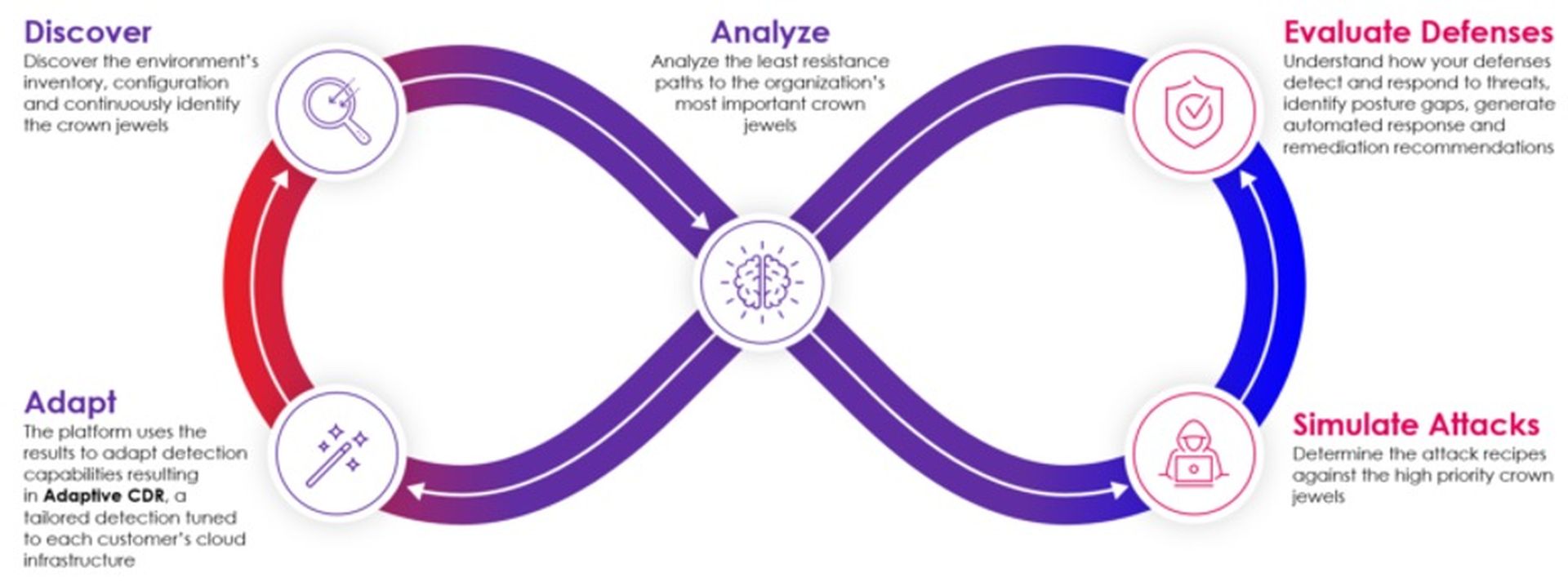
Skyhawk’s Continuous Autonomous Purple team does exactly that. An AI-based Red Team “fights” an AI-based Blue Team to find vulnerabilities in the cloud attack surface. Where the red team gets past the blue team, we look at those issues and then prioritize what needs to be fixed based on the business value of the asset behind it. The specifics of the process are as follows:
The report mentions, “Autonomous Adversarial Emulation (AAE) systems have the ability to learn from their environment and continuously enhance their capabilities, thus enabling them to proactively and cost effectively simulate threat actor behavior that is tailored to an organization’s unique ecosystems.”
Skyhawk’s Purple Team evaluates the security of your cloud by attacking your platforms simulates how a threat actor will behave, and how our CDR will respond. This continuous feedback is what allows for continuous improvement in overall cloud security. Additionally, cloud environments are always changing, and this continuous evaluation and feedback ensures that as your cloud architecture changes, so does your cloud security.
Gartner® Recommended Actions
How can I implement the Gartner® recommendations?
Skyhawk Security makes implementing Gartner® recommendations very easy as the platform delivers an AI-based Autonomous Purple Team which adapts your cloud security to changing threats and changing cloud architectures, ensuring your cloud security and cloud architecture are consistently aligned.
Skyhawk’s Cloud Threat Detection and Response (CDR) leverages advanced machine learning models to detect threats in real-time to prevent threats from evolving to cloud breaches, including the detection of unknown unknowns. Skyhawk’s platform is supervised by our security experts who ensure the models are trained with the right data to detect the threats in your cloud. Check out this blog for more information.
Get Started with Skyhawk Today
Skyhawk has two free offerings that you can use today to understand how we can stop cloud threats from becoming cloud breaches.
You can read the full report at www.gartner.com.
Gartner, Emerging Tech Impact Radar: Preemptive Cybersecurity by Luis Castillo, Lawrence Pingree, Carl Manion, Ruggero Contu Published November 25, 2024.
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.




